Kruptos 2 Professional for Windows x64 is an easy to use encryption program that uses 256-bit encryption to password protect your private files and prevent them from being modified, read or even accessed without the correct password. With Kruptos 2 Professional you can password protect all your sensitive personal and commercial information including your photos, movies, credit card data, tax returns or any other private document.
Omega DB Scanner Standalone is an out-of-box, software-only solution. This Standalone and Free Edition is a simple client-side solution that is deployed on the user's PC and easily scans the security posture of your Oracle database. Run the whole scan set on the target database, or just run a single vulnerability scan, the assessed result in both summary and full will give you a clear picture of the scanned items security configuration.
Record every detail of computer usage and Internet activity. See exactly what computer users looked at, all Web sites visited, and everything typed - can be used at home, or in your office. View recordings from the computer installed on, and remotely from any computer via the Internet - no technical knowledge is needed. Remains completely invisible at all times.
A files hash calculator on Windows. fHash can calculate and verify MD5, SHA1, SHA256 and CRC32 digests of files. fHash supports drag and drop and can integrate into Explorer's context menu. Fast and easy to use. English and Chinese versions.
Command-line Tool to Hide Your Computer on Network
Passwords and other information can be transferred to other applications automatically. You will have fewer login problems. You'll never have to worry about forgetting a password or losing access to critical applications or web sites. All you need to remember is one master password.
GiliSoft Full Disk Encryption's offers encryption of all disk partitions, including the system partition.Through password protecting a disk, disk partition or operating system launch, the program disables any unauthorized reading/writing activity on your disk or PC, restricts access and launch of specific disks and files.
IE PassView is a small utility that reveals the passwords stored by Internet Explorer Web browser. It supports all versions of Internet Explorer, from version 4.0 and up to 8.0. For each password that is stored by Internet Explorer, the following information is displayed: Web address, Password Type (AutoComplete, Password-Protected Web Site, or FTP), Storage Location, and the user name/password pair.
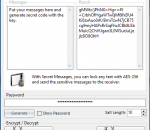
Secret messages is a software which is designed to encrypt your messages before you send them. If you would like to send message online, then you should not worry on how you can prevent unauthorized access to the messages. There are some people out there who are eager to hack your messaging account and read the information you are trying to send. The program generates encryption images which hide your message before you can send.
iSunshare Outlook Email Password Genius is the easy-to-use Outlook email password recovery tool for free download, which enables users to recover all saved email account password from Microsoft Outlook, including Gmail, Hotmail, Outlook, Live email, and etc.
With one simple mouse click, Square Privacy Cleaner allows you to erase Windows traces, recent opened documents, prefetch files, clipboard cache, MRU lists, temp folders, junk files, making PC operation fast and smooth. You can clean Internet traces, like cookies, history and cache of popular web browsers, such as Mozilla Firefox, Internet Explorer, Opera, Google Chrome.